
Hollow Pentesting
Confidently using AI in your Pentests. Hollow Testing.

Confidently using AI in your Pentests. Hollow Testing.

Chaining three issues to gain root from a low privileged user.
File Folding is a technique that moves a file into hex, and that hex is broken into folder file names in a fashion that can be reconstructed.
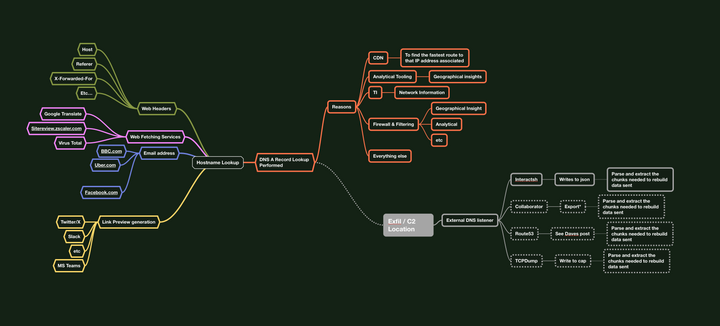
Data-Bouncing - The art of indirect exfiltration. Using & Abusing Trusted Domains as a 2nd Order Transport.

The idea behind three word passwords as a concept is in my opinion a nice nudge in the right direction, In a perfect world, a passphase or a sentence

Cross-referencing acquired credentials against public known, known bad credentials in a bid to really hit home the cultural change required. or just fully breaking down a target.