
Hollow Pentesting
Confidently using AI in your Pentests. Hollow Testing.

Synology DSM 7.3.2
Chaining three issues to gain root from a low privileged user.

CVE-2025-37186 HP
The HP Aruba VIA VPN client for Linux contains a local privilege escalation vulnerability that allows any unprivileged local user to gain root access. - CVE-2025-37186 - Another Scalp for Raptor

Hacklore ...
What Hacklore get's wrong. and the precursor to https://lolwifi.network
Ghosted.
Ghosted Domains coming to haunt you, one more check for your scanners, vendor assurance, OSINT, Supply chain, Appsec and all the rest of that good stuff.

Poll-Dancing & Age Verification
Poll-Dancing & Age Verification - a critical view of yougov's obvious biased framing of the age verification shit-show

Sunsetting Domains
What to do when you no longer need a domain

Amature.
The wrong people in the room when the decisions where made to reduce citizen data security.
The BYOD Post.
BYOD Problem, options.

Files, Folders & Fun (revisited)
Playing with folder resolution to build a better pretext

The Cost of Expiration
Who needs to know when a domain has expired ? It Depends, and it Deepens.
File Folding.
File Folding is a technique that moves a file into hex, and that hex is broken into folder file names in a fashion that can be reconstructed.

Untrusted Wi-Fi Networks, Advice for All.
Nine words unpacked.
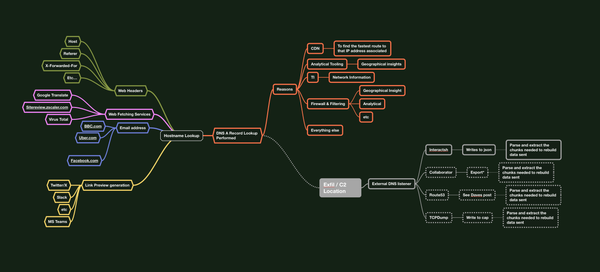
Data-bouncing
Data-Bouncing - The art of indirect exfiltration. Using & Abusing Trusted Domains as a 2nd Order Transport.

Securing Ghost Blog Authentication with Cloudflare's ZeroTrust Access Policy
How to implement MFA in Ghost Blog with Cloudflare's Zerotrust Access Policy.

Three-Word Password Attacks
The idea behind three word passwords as a concept is in my opinion a nice nudge in the right direction, In a perfect world, a passphase or a sentence

Get TI from historical breach data?
We can do more with breach data.

Identity Inheritance via expired domains
I wonder if any of these leaked email address domains are expired, and I wonder if I can buy them and inherit the identities associated with them via password resets

Inference.
The way we leak information will eventually change...

'ExpLoading'
If you have ever dismissed a search order binary plant attack because the folder from where it takes place doesn’t allow for writes without elevation?

Bigger Benefits of Password Cracking
Visibility everywhere yeilds a better understanding of work working, or work needing more support or new approaches. this is that for AD passwords en-mass.

Paying or Preventing Ransom Payments
Don't make criminals of victims, think a little harder on this problem.

DNS Security TXT
DNS Security TXT record A method to hold security contact signposting from an authoritative position - from Casey Ellis & myself https://dnssecuritytxt.org/?tc

Vertical Vulnerability Managment
Vulnerabilities are technology, security and risk vertical, as should be the management.

The Internet Facing Velocity Problem
It's probably faster to find a flaw in all IPv4 Assets with Open-source attack and exploit validation tools than it is for someone internal to hunt down the owners, maintainers and appropriate people for remedial actions - The Internet Facing Velocity Problem

DNS Stewardship
DNS Stewardship, the art of controlling internet facing projects from conception.

OWASP Top 10 - 2021
This post is as much as an internal sit-rep as it is one for others to witness, share and challenge, I'm trying to understand the Top10's value eleven years on, the current top10 (2021) is in draft and open for comment, I've put my comments here, as well as the opening to this conversation on github

A Method for identifying .onion associated IP addresses
This post is in theory, sound, however executing it would take real collaboration that probably doesn't exist and due to the benefits of tor to certain operations is going to be counterproductive,but, something to think about all the same

Imposter.
Thoughts on Imposter Syndrome, In summation; Imposter Syndrome is the consequence of poor support.

Publicker.
Cross-referencing acquired credentials against public known, known bad credentials in a bid to really hit home the cultural change required. or just fully breaking down a target.
Privacy Engineering ?
Grammarly taking more data than it should, a exploration and musings over the idea of privacy engineering in conjunction with application security assessments

Folders, Files & Canary Fun

Installation Security Considerations
A little tip for defence when software is installed outside of default locations. A little tip for offence when software is installed outside of default locations.

Active Directory Network Agents and not-good deployments
That’s a Nice Palo-Alto Firewall Forescout Active Directory Integrated Network Appliance you have ther